Blog
January 28, 2019
Installing Wildfly on Docker is a smart choice. In this blog, we break down how to set up Wildfly for Docker and start deploying today.
Back to topBefore Getting Started With Wildfly + Docker
Please ensure firewall disable/enable commands (if issued in production systems) align with the best practices and guidelines at your site. This blog instructs to expose ports 8080 and 9990 for conventional use of Wildfly OSS product.
Additionally, if you prefer not to disable SELinux, please refer to the audit2allow/audit2why toolset to identify and correct areas where/why Wildfly is being blocked by SELinux. This is just in case a policy change is required to ensure that the operations being permitted does not pose a security threat.
Back to topHow to Set Up Wildfly For Docker
1. Install Wildfly
In order to install WildFly 14, we will use Oracle VirtualBox to create a vmdk and install the Red Hat CentOS 7 iso image.
Use setenforce 0 to enter permissive mode:
setenforce 0
Then use systemctl to stop and disable the firewall daemon:
systemctl stop firewalld
systemctl disable firewalld
In order to access the vm from a network terminal rather than a console, run the dhclient as superuser:
sudo dhclient
Update the distro, install wget and ntp, set your timezone without using root user privileges, and create an openlogin login {ol} and add it to the wheel group for sudo privs:
yum update
yum install wget
sudo useradd ol -m
sudo passwd ol
sudo usermod -aG wheel ol
sudo yum install ntp
sudo timedatectl set-timezone America/Los_Angeles
Install the openjdk version "1.8.0_191" with devel. (This is important!)
sudo yum install java-1.8.0-openjdk
sudo yum install java-1.8.0-openjdk-devel
install wget-1.14-15.el7_4.1.x86_64
install unzip
install nano-2.3.1-10.el7.x86_64
Finally, you are ready to install WildFly 14:
wget http://download.jboss.org/wildfly/14.0.1.Final/wildfly-14.0.1.Final.zip
sudo unzip wildfly-14.0.1.Final.zip -d /opt/
2. Configure Wildfly
Now we need to edit the conf file:
sudo nano /opt/wildfly-14.0.1.Final/bin/standalone.conf
Add:
JBOSS_HOME="/opt/wildfly-14.0.1.Final"
You can start WildFly 14.0.1 in its simplest configuration with standalone.xml:
sudo ./standalone.sh -b=0.0.0.0 -bmanagement=0.0.0.0
You can also start WildFly 14 with an alternate configuration:
sudo ./wildfly-14.0.1.Final/bin/standalone.sh --server-config=standalone-full-ha.xml
3. Add a user
Now you are ready to add user to the WildFly application server:
./add-user.sh
[ol@localhost bin]$ sudo ./add-user.sh
What type of user do you wish to add?
a) Management User (mgmt-users.properties)
b) Application User (application-users.properties)
(a):
Enter the details of the new user to add.
Using realm 'ManagementRealm' as discovered from the existing property files.
Username : ol
Password recommendations are listed below. To modify these restrictions edit the add-user.properties configuration file.
- The password should be different from the username
- The password should not be one of the following restricted values {root, admin, administrator}
- The password should contain at least 8 characters, 1 alphabetic character(s), 1 digit(s), 1 non-alphanumeric symbol(s)
Password :
WFLYDM0099: Password should have at least 8 characters!
Are you sure you want to use the password entered yes/no? yes
Re-enter Password :
What groups do you want this user to belong to? (Please enter a comma separated list, or leave blank for none)[ ]: ManagementRealm
About to add user 'ol' for realm 'ManagementRealm'
Is this correct yes/no? yes
Added user 'ol' to file '/opt/wildfly-14.0.1.Final/standalone/configuration/mgmt-users.properties'
Added user 'ol' to file '/opt/wildfly-14.0.1.Final/domain/configuration/mgmt-users.properties'
Added user 'ol' with groups ManagementRealm to file '/opt/wildfly-14.0.1.Final/standalone/configuration/mgmt-groups.properties'
Added user 'ol' with groups ManagementRealm to file '/opt/wildfly-14.0.1.Final/domain/configuration/mgmt-groups.properties'
Is this new user going to be used for one AS process to connect to another AS process?
e.g. for a slave host controller connecting to the master or for a Remoting connection for server to server EJB calls.
yes/no? yes
To represent the user add the following to the server-identities definition
4. Allow Access to Wildfly
WildFly runs on port 8080 and 9990, so you will need to allow this port to access WildFly from an outside network. Domain API: http://:9990/management Admin Web Console: http://:9990/console You can do this by running the following commands:
sudo firewall-cmd --zone=public --add-port=8080/tcp --permanent
sudo firewall-cmd --zone=public --add-port=9990/tcp --permanent
sudo firewall-cmd --reload
You are now ready to access WildFly:
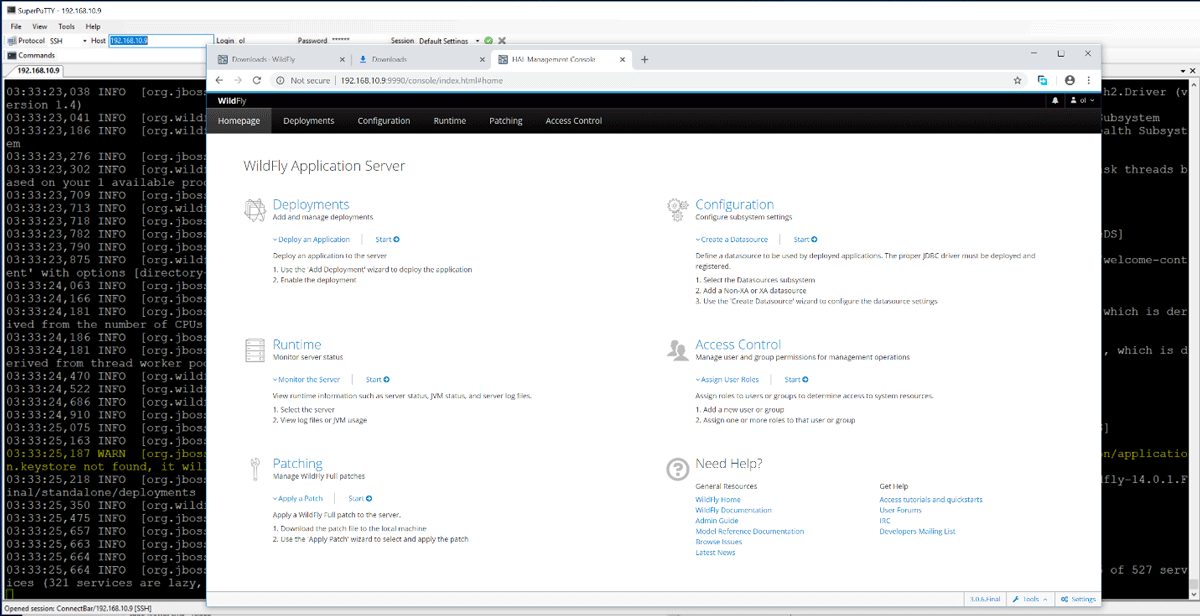
5. Configure the JDBC Connection
But wait! We need to configure JDBC connection to access an external postgres server! For that, you'll need the current version of the JDBC driver.
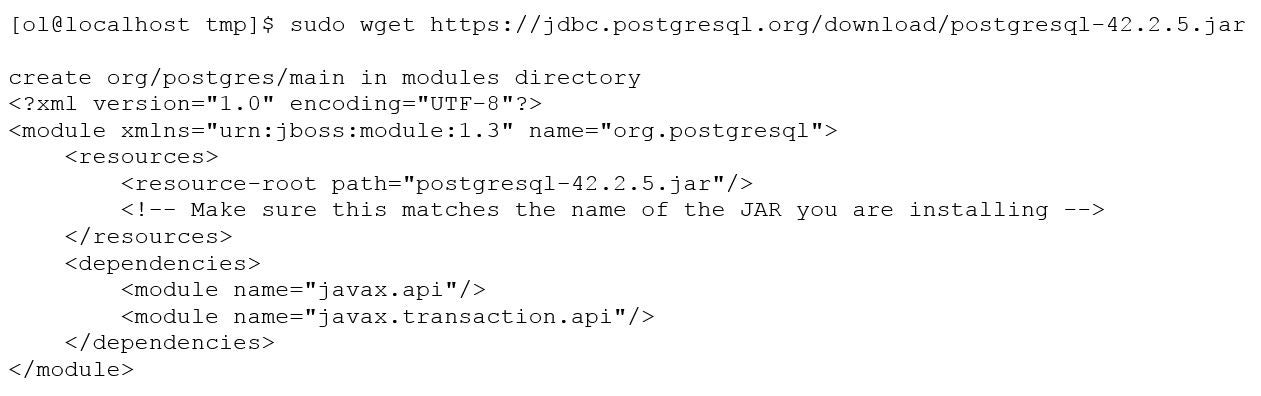
Go to /standalone/configuration directory in your WildFly installation directory. Open standalone.xml. (It's the default configuration file used by the standalone server.) Search "datasource" to go to the right part. In the <datasources> element, you need to add both <driver> for PostgreSQL and <datasource>:
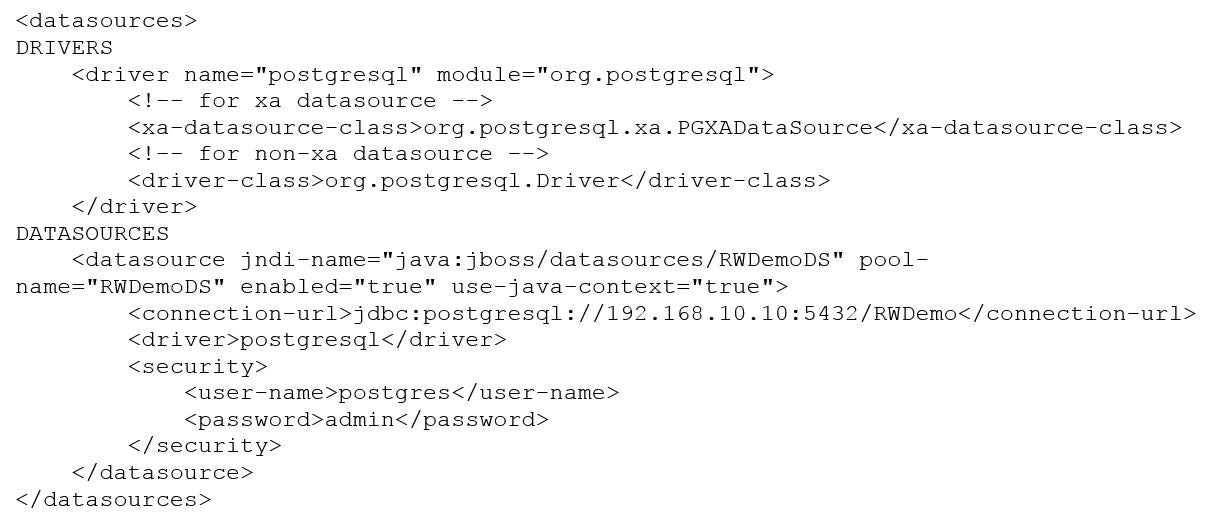
Almost done. We also need to add Listener for mod_jk incoming requests:
<server name="default-server">
<ajp-listener name="defaultajp" socket-binding="ajp"/>
<http-listener name="default" socket-binding="http" redirect-socket="https" enable-http2="true"/>6. Use Wildfly on Docker Images
Build the Docker image as follows.
docker build -t wildfly14.0.1:latest .
docker build -t registry.openlogictest.local:5000/wildfly14.0.1:latest .
docker login registry.openlogictest.local:5000
PS C:\Users\s.b\Documents\docker_builds> docker login registry.openlogictest.local:5000
Authenticating with existing credentials...
Login Succeeded
Next, we push the image to a registry and tag it!
docker push registry.openlogictest.local:5000/wildfly14.0.1:latest
docker tag wildfly14.0.1:latest registry.openlogictest.local:5000/wildfly14.0.1:latest
On slow networks for big Docker images, it is possible to get TLS handshake timeouts:
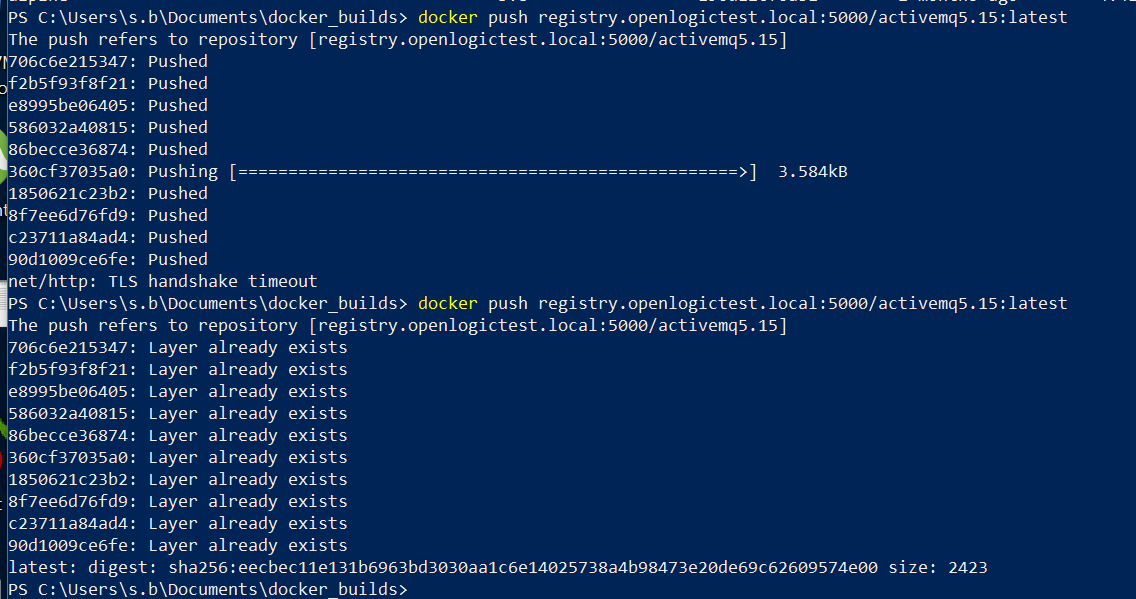
On inspection, the Docker image shows up as follows:
PS C:\Users\s.b\Documents\docker_builds> docker image inspect registry.openlogictest.local:5000/wildfly14.0.1:latest
[
{
"Id": "sha256:a7a00b9866143222403e151fcfcae14be45ee1293a5807036106e4b0f5483d6b",
"RepoTags": [
"wildfly14.0.1:latest",
"registry.openlogictest.local:5000/wildfly14.0.1:latest"
],
"RepoDigests": [
"registry.openlogictest.local:5000/wildfly14.0.1@sha256:4b73aeeb661a4a9e57db8d5dda3418baa3ba1338b7054d34249993c8cde09387"
],
"Parent": "sha256:c9fc8026cd537929889307d0b3b2af666de341819758c7ad091da553d7c96a38",
"Comment": "",
"Created": "2018-12-09T07:06:39.5334145Z",
"Container": "fdabd105bcce8d87a0347b8d9f3a60463571838e5d07fb1d062770f1807a9580",
PS C:\Users\s.b\Documents\docker_builds> docker image list
REPOSITORY TAG IMAGE ID CREATED SIZE
wildfly14.0.1 latest a7a00b986614 3 hours ago 651MB
registry.openlogictest.local:5000/wildfly14.0.1 latest a7a00b986614 3 hours ago 651MB
activemq5.15 latest dbeded55f300 8 hours ago 570MB
registry.openlogictest.local:5000/activemq5.15 latest dbeded55f300 8 hours ago 570MB
httpd246 latest 6265b75efecd 23 hours ago 258MB
registry.openlogictest.local:5000/httpd246 latest 6265b75efecd 23 hours ago 258MB
postgres11.1 latest c1551be063ce 24 hours ago 71.7MB
Back to top
How to Use Wildfly For Microservices
Did you know you can also use Wildfly for microservices authentication? In our recent white paper, find out why and how to use Wildfly for mutual TLS authentication for microservices.
Plus, get a step-by-step tutorial for implementing Mutual TLS authentication.
Back to top